Şu anda adlı kullanıcıyı takip ediyorsunuz
Kullanıcıyı takip etmede hata.
Bu kullanıcı kullanıcıların kendisini takip etmesine izin vermiyor.
Zaten bu kullanıcıyı takip ediyorsunuz.
Üyelik planınız sadece 0 takibe izin veriyor. Buradan yükseltme yapın.
başarılı bir şekilde takipten çıkarıldı
Kullanıcının takip edilmesinde hata.
adlı kullanıcıyı başarılı bir şekilde tavsiye ettiniz
Kullanıcıyı tavsiye etmede hata.
Bir şeyler yanlış gitti. Lütfen sayfayı yenileyin ve tekrar deneyin.
E-posta başarılı bir şekilde doğrulandı.


islamabad,
pakistan
Şu anda burada saat 1:15 ÖS
Şubat 10, 2012 tarihinde katıldı
0
Tavsiye
Muhammad H.
@has00ali20
3,8
3,8
100%
100%

islamabad,
pakistan
%100
Tamamlanmış İş
%100
Bütçe Dahilinde
%100
Zamanında
%33
Tekrar İşe Alınma Oranı
Software Developer | Solution Architect
Muhammad H. ile işiniz hakkında iletişime geçin
Detayları sohbet üzerinden tartışmak için giriş yapın.
Portföy
Portföy


Capital Zam Zam
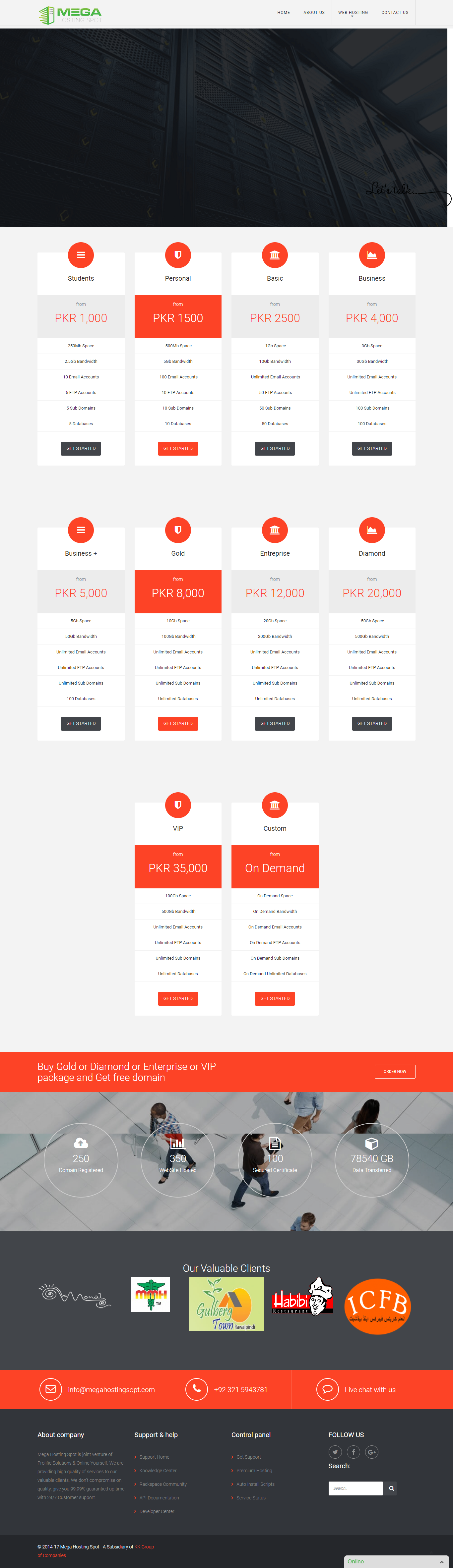

Mega Hosting Spot
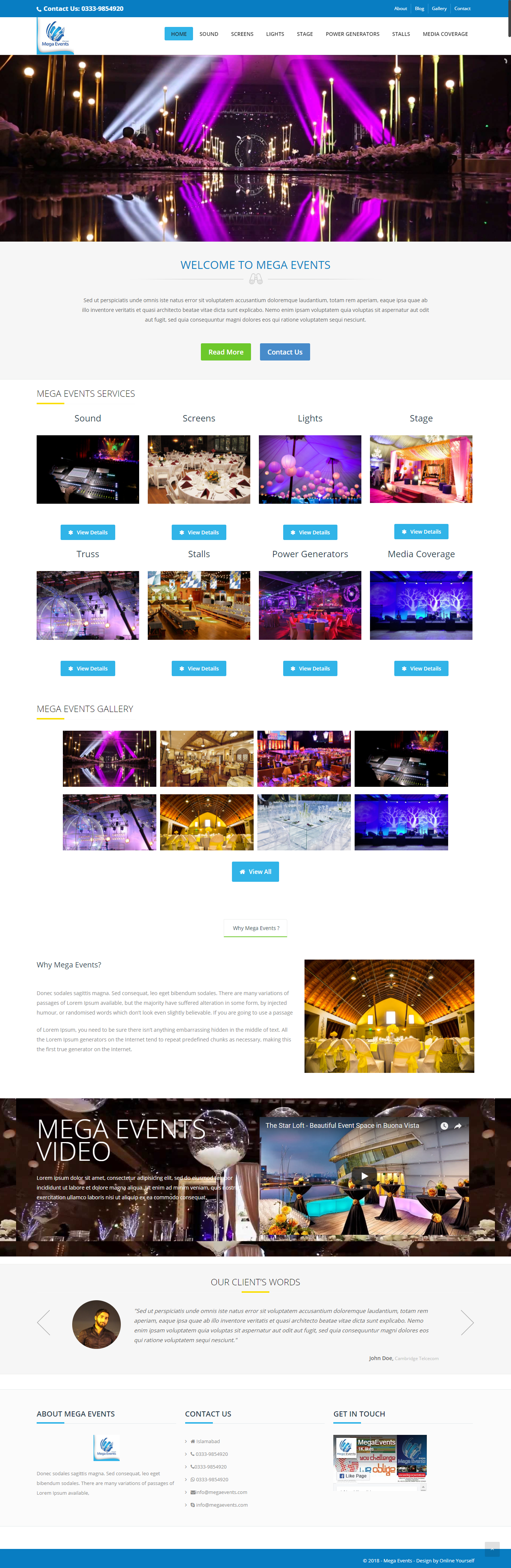

Mega Events


Gulberg Town
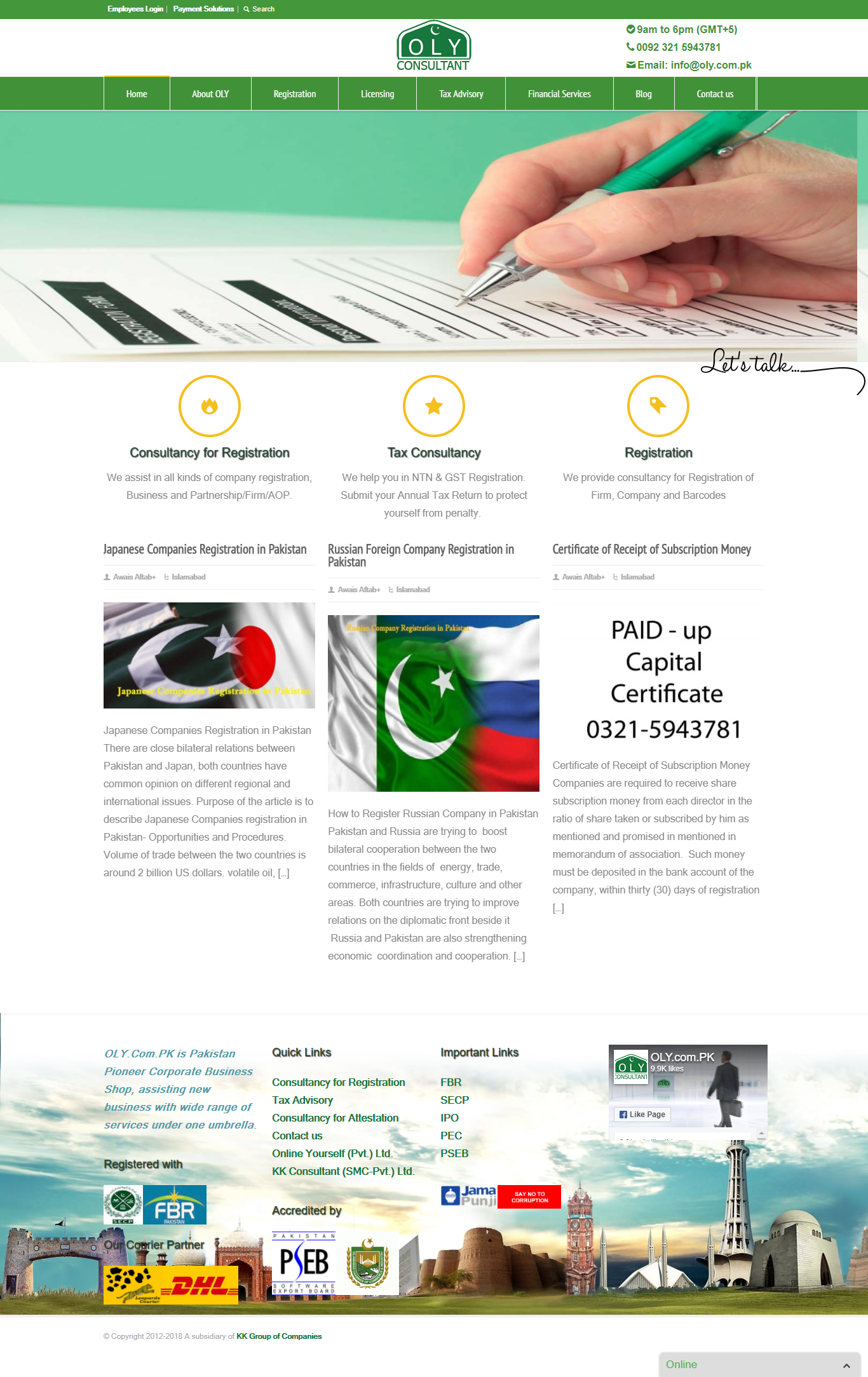

OLY Consultant


HYPER PAY


Capital Zam Zam

Mega Hosting Spot

Mega Events


Gulberg Town

OLY Consultant


HYPER PAY
Değerlendirmeler
Değişiklikler kaydedildi
2 değerlendirme içinden 1 - 2 arasındakiler gösteriliyor
$462,00 USD
Java
SQL
HTML5
JSON
Encryption


•
$60,00 USD
Python
Linux
Django
Software Architecture


•
Deneyim
AQTech (http://aqtechco.com)
Mar 2012 - Şu anda
Currently Working as PHP, Java and Mobile Developer.
Working as part of Vendor Telecom Company, Development of VAS services and FS Project
Involved in pure hard core development and performed R&D task on new development technologies.
Eğitim
MS Information Security
(2 yıl)
BS Computer Science
(4 yıl)
Nitelikler
Advanced Java EE Training
prudsol.com
2013
Advance Java EE Concepts, Design Patterns
Web Vulnerabilities – Attacks, Exploits and Mitigation
2015
Malware Behavior Analysis Using Memory Forensics
COMSATS Islamabad
2015
Memory Forensics used to analyse the behavior of malware from within memory
Yayınlar
Unfolded Competitive Legacy of Operating Systems
The Linux VS Windows is a topic for discussion since the beginning of computers. Years have passed but still it's hard to say which OS is the best on the other. We evaluate both operating systems at abstract level for better understanding what are the common features provided operating systems and where operating systems dominates each other.
Attribute Based Access Control for Outsourced Provenance Graph
Thesis on Access Control
Automation era prevailing in today’s environment is most exposing to cyber threats. Provenance captures the information needed to attribute ownership and determine, among other things, the quality of a particular data set. Provenance shows entire history from origin to present but an attacker try to exploit the provenance record by obtaining unauthorized access to the system. In this research work we introduced attribute based access control for provenance record.
Muhammad H. ile işiniz hakkında iletişime geçin
Detayları sohbet üzerinden tartışmak için giriş yapın.
Doğrulamalar
Sertifikalar
Benzer Freelancerlara Göz Atın
Davet başarılı bir şekilde gönderildi!
Teşekkürler! Ücretsiz kredinizi talep etmeniz için size bir bağlantı gönderdik.
E-postanız gönderilirken bir şeyler yanlış gitti. Lütfen tekrar deneyin.
Ön izleme yükleniyor
Coğrafik konum için izin verildi.
Giriş oturumunuzun süresi doldu ve çıkış yaptınız. Lütfen tekrar giriş yapın.